Tech & Innovation
ABC’s of protecting SMBs in SEA against malicious mining
As the symptoms and consequences of malicious mining are less obvious and less immediate than ransomware and phishing attacks, it’s easy for SMBs to disregard it as a mere technical issue. However, its aftermath is costly in the long run.

Tech & Innovation
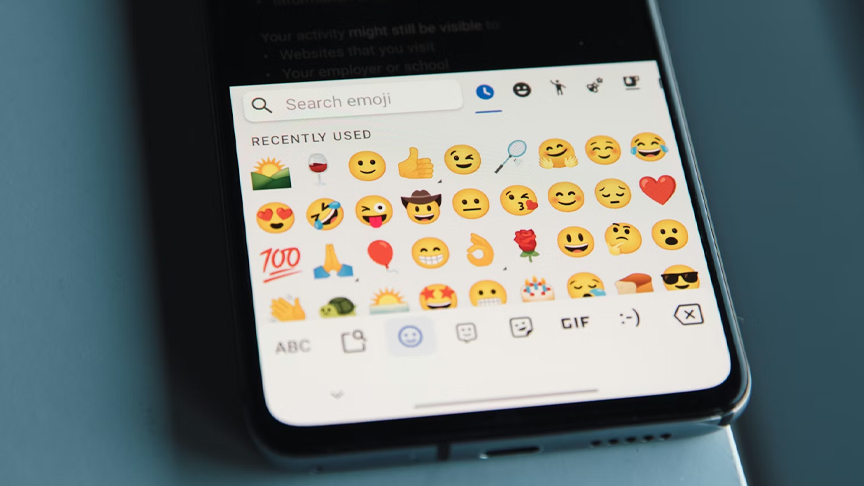
Should emojis be used in workplace communications?
Messages with no emojis were clearly the winner, making the sender appear more competent and professional.
Tech & Innovation
Augmented reality menus may help restaurants attract more customers, improve brand perceptions
AR menus can significantly increase customers’ interest in visiting a restaurant and may result in more positive word-of-mouth marketing, when compared to printed or QR-code menus.
Tech & Innovation
Epson launches SureColor-S7130 as latest addition to acclaimed SC S-Series of eco-solvent printers
With the equipment segment expected to capture more than 75% of the market revenue in Asia Pacific’s commercial printing market, where there’s also a growing demand for short-run and on-demand printing, the SC-S7130 aims to meet evolving needs by empowering businesses to operate more competitively and sustainably.
-

 Strategies3 weeks ago
Strategies3 weeks agoRenting out your place? Human connection key to a successful holiday rental
-

 BizNews3 weeks ago
BizNews3 weeks agoIf you’re a perfectionist at work, your boss’ expectations may matter more than your own, research finds
-

 Tech & Innovation3 weeks ago
Tech & Innovation3 weeks agoShould emojis be used in workplace communications?
-

 BizNews3 weeks ago
BizNews3 weeks agoProfit alone is a poor measure of success, study shows companies can look efficient while harming the planet
-

 BizNews3 weeks ago
BizNews3 weeks agoReminder to marketing people: Missing information can misinform
-

 BizListing2 weeks ago
BizListing2 weeks agoCombo of café vibe with Filipino and Italian dishes as biz model of Yellow Bird resto
-

 BizNews5 days ago
BizNews5 days agoLong-serving CEOs may weaken innovation, study finds
-

 Ethical Biz1 day ago
Ethical Biz1 day agoCanon Marketing Philippines leads Brigada Eskwela to help prepare Lagro High School for new school year