Tech & Innovation
Ultimaker launches software solution, Ultimaker Essentials
New subscription-based platform puts software at the heart of the enterprise and includes new eLearning platform to bridge widening knowledge gap.

Tech & Innovation
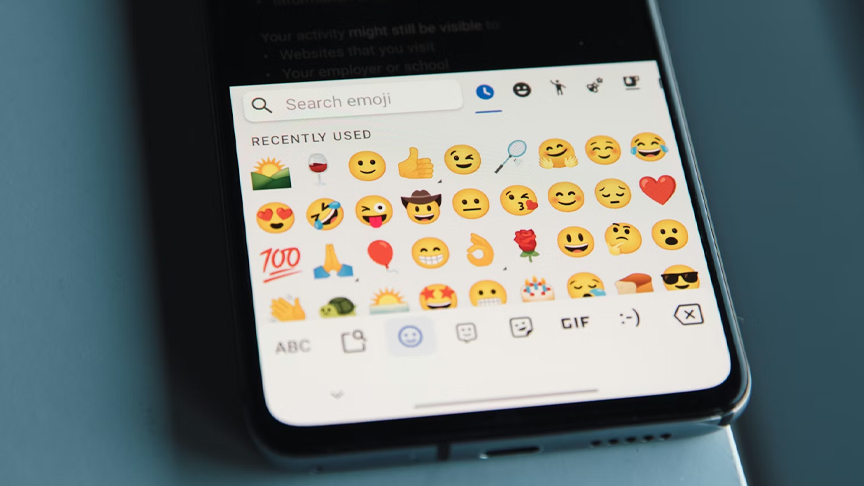
Should emojis be used in workplace communications?
Messages with no emojis were clearly the winner, making the sender appear more competent and professional.
Tech & Innovation
Augmented reality menus may help restaurants attract more customers, improve brand perceptions
AR menus can significantly increase customers’ interest in visiting a restaurant and may result in more positive word-of-mouth marketing, when compared to printed or QR-code menus.
Tech & Innovation
Epson launches SureColor-S7130 as latest addition to acclaimed SC S-Series of eco-solvent printers
With the equipment segment expected to capture more than 75% of the market revenue in Asia Pacific’s commercial printing market, where there’s also a growing demand for short-run and on-demand printing, the SC-S7130 aims to meet evolving needs by empowering businesses to operate more competitively and sustainably.
-

 Strategies2 weeks ago
Strategies2 weeks agoRenting out your place? Human connection key to a successful holiday rental
-

 BizNews2 weeks ago
BizNews2 weeks agoIf you’re a perfectionist at work, your boss’ expectations may matter more than your own, research finds
-

 Tech & Innovation2 weeks ago
Tech & Innovation2 weeks agoShould emojis be used in workplace communications?
-

 BizNews4 weeks ago
BizNews4 weeks agoIn-aisle store displays might crowd shoppers and reduce overall sales
-

 BizListing4 weeks ago
BizListing4 weeks agoClaim to fame: Fried chicken built Lolo Claro’s
-

 BizNews2 weeks ago
BizNews2 weeks agoProfit alone is a poor measure of success, study shows companies can look efficient while harming the planet
-

 BizNews2 weeks ago
BizNews2 weeks agoReminder to marketing people: Missing information can misinform
-

 BizListing1 week ago
BizListing1 week agoCombo of café vibe with Filipino and Italian dishes as biz model of Yellow Bird resto